PRODUCT

Smarter Biometrics, Stronger Digital Identity.
VIEW ALL
product finder
solution
case study
support
Company

Identifying the World. Easily, Securely.


years of solid experience
20+
.jpg)
400+
customised projects



EN
.avif)

The battle for the most reliable authentication method has been ongoing since security systems first became available. With such a wide variety of authentication methodologies to pick from, it can be tough to tell which one is the safest.
From username and password combinations to mobile phone verification to biometric identification, every form of authentication comes with advantages and disadvantages in terms of safety. So, which type of authentication is most secure? Let’s take a look at some of the most popular options and see which one comes out on top.
Passwords have a lengthy history that has evolved. Passwords were originally used in military applications and were known as the "Roman password." It was intended to be a system used by soldiers. The chosen password was a watchword that had to be delivered to the sentries on a daily basis. Today, passwords have become an integral part of our everyday lives.
For businesses looking for a low-cost option, usernames and passwords are a great choice because of how simple they are to implement. The process of creating usernames and passwords usually has one or more steps that might include creating new accounts, joining users with those accounts, assigning a password to each user, examining the durability of those passwords, and other security procedures. It's simple, easy to use, and relatively low in cost.
However, passwords and usernames are known to not be the most secure method out there, no matter how much we love them. If users don't use strong password practices, it's easy to guess or hack their passwords. Also, because usernames and passwords are easy to set up, they might not be enough security for businesses that deal with sensitive information.
Despite its drawbacks, username and password authentication is widely accepted for many businesses. If you’re looking to implement this type of authentication into your security system, it’s important to take steps to protect against password guessing and hacking. If you want to make sure your data and infrastructure are safe, you may want to consider spending money on extra security measures like encryption and two-factor authentication.
In recent years, mobile authentication has become a popular choice for businesses looking to improve their security. This type of authentication process typically involves sending an SMS code to users’ mobile devices which they then enter to access their account.
While this method provides an extra layer of security, it can also be tricky to implement and may result in slower sign-in times. Additionally, mobile authentication requires users to provide their phone numbers which can pose privacy concerns for some businesses.
Several factors determine how secure a mobile authentication method is. Some of these include what type of information is sent to the cloud, how it's encrypted, and how the device's operating system handles the data. Overall, mobile authentication is a viable security solution if implemented correctly and used in conjunction with other options.
Biometric authentication method is arguably one of the most secure methods available today—no two fingerprints are alike after all! Biometric technologies like fingerprint recognition, facial recognition, iris recognition, voice recognition, etc., use physical characteristics unique only to that person as identifying factors which makes it almost impossible for any other person or entity—even hackers—to gain access without those biometric credentials.
Biometric authentication methods are classified into two types of biometric systems:
These are biometrics that is directly related to the human body and its functions, such as human face, fingerprints, irises, and voices.
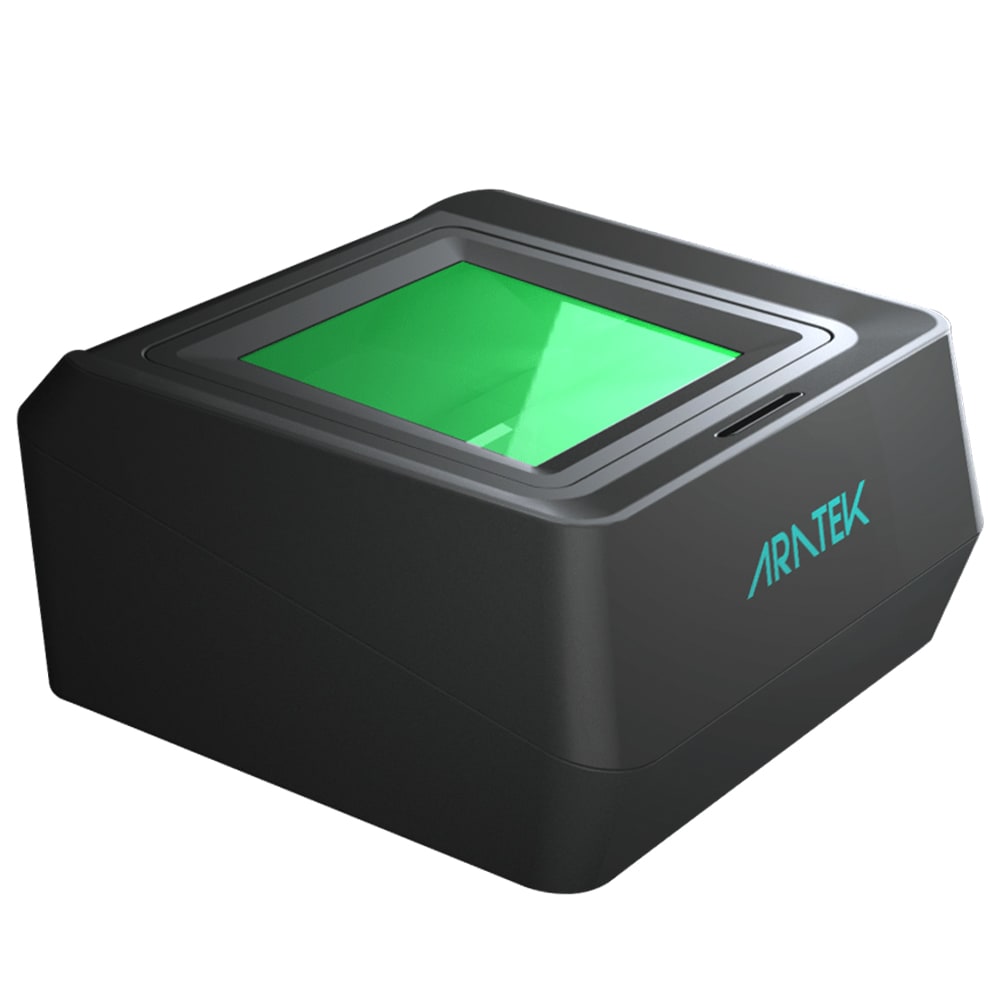
In this method of authentication process, the user has to provide their biometric identifiers via biometric devices such as a fingerprint scanner, camera, or speaker, which records their biometric physical attributes and compares them to their stored biometric data. This type of secure authentication, which is heavily based on physical biometric characteristics, is regarded as one of the most reliable methods for effectively preventing fraud and identity theft.
These detect the way people interact with their environment which usually involves some physical tasks performed repeatedly which include gaits, keystrokes, handwritten signature, and mouse dynamics which capture how a user moves. This method of biometric authentication which is based on behavioral characteristics can easily be changed which means it is not as reliable as physiological biometrics.
Biometric methods, on the other hand, can be vulnerable if not properly secured or protected. For example, if someone manages to steal your fingerprint scanning data, they may be able to access your accounts or facilities without any additional verification steps. As a result, the liveness detection of biometric data, as well as proper encryption, are critical to ensuring that your biometrics and biometric system are secure and cannot be easily stolen or spoofed by hackers.
Overall, biometric authentication is a highly secure authentication method that is favored by many businesses today. However, it is important to carefully consider which type of biometric authentication is best suited for your business and its security needs, as well as which additional measures you can take to further secure your biometric data.
In addition, it is also important to understand that even the most sophisticated authentication methods are not infallible and can be vulnerable to certain types of attacks, which is why it is essential to continuously improve your security measures and stay up-to-date on the latest security trends to protect your business against potential threats.
Two-Factor Authentication (2FA) requires users to enter two pieces of information to access an account - typically something you know (like a password) combined with something you possess (like a phone or email). This makes it more difficult for hackers to gain access to accounts because even if they manage to guess or steal a user’s password, they still need that second piece of info which is harder to get. The token-based authentication which is a part of 2FA will send an authentication code to the registered mobile device or email account which needs to be entered before the user is granted access to the account or system.
Multi-factor authentication (MFA), which is similar to 2FA, involves using multiple different factors - typically something you know (like a password), something you are (like biometric identifiers), and something you have (like a mobile device).
The difference between MFA and 2FA is that while the latter only requires one additional piece of information to access a user's account, MFA can require multiple factors such as passwords and a biometric or digital token, which is more difficult to mimic when compared to traditional security methods. Physical token-based MFA is another method that uses physical devices, such as keyfobs or USB tokens to generate one-time passwords. This extra layer of security can help prevent account hijacking and other common forms of attacks. This makes multi-factor authentication much more challenging for hackers to gain access to a user's account and information.
Multi-Factor Authentication (MFA) adds additional layers of security by requiring users to provide multiple pieces of information to access an account or building. In the airport, for example, you might have to enter your ticket number, which you know, along with your passport, which you have, and a biometric scan of your fingerprint or face, which you are, to gain access to your flight. Multi-factor authentication makes it more difficult for hackers to break into accounts and systems because even if they steal one piece of information, they still need the other pieces which are harder to obtain.
While 2FA and MFA are effective in ensuring that only authorized users can access accounts or facilities, it is important to note that these processes do not necessarily provide bulletproof security. For example, if a user’s device is hacked, they may inadvertently give away their 2FA or MFA credentials which can be used by hackers to gain access to their accounts. Additionally, users may be tempted to share or store their second-factor information which leaves them open to account takeovers if it is compromised.
As a result, it is essential for businesses to have strong cyber security and physical access control measures in place and to continuously monitor for potential threats. With the right protocols in place, businesses can implement 2FA or MFA without compromising security. Ultimately, which authentication method is the most secure will depend on your specific needs and the security level required for your business. However, by leveraging a combination of 2FA or MFA with other best practices, businesses can minimize the risks and protect their accounts, data, and other valuable assets.
As you can see, there isn't one single "right" answer when it comes to selecting an authentication type; each has its pros and cons depending on your needs and budget constraints. While some authentication methods, such as username and password credentials, can be relatively easy to implement, they are also often subject to common vulnerabilities such as phishing attacks or brute force attempts. Other methods, such as two-factor authentication, may be more secure in some cases but can also introduce added complexity that can make them difficult to use in some contexts.
Many experts agree that multi-factor authentication with biometric security process is currently the best way forward since it offers increased levels of protection from potential hacking attempts without breaking the bank in terms of implementation costs, it still remains important to keep a close eye on your security protocols and be prepared to adapt as new threats emerge.
So, if you want to improve your company's security, you should think about which authentication method will best meet your needs while also providing a seamless user experience. Contact a security expert today to discuss your options and begin the process of making your company more secure.
Authentication is the process of verifying that a person or device is who or what it claims to be. This typically involves confirming a user’s identity through some type of identifying factors, such as a username and password combination, biometric data like fingerprints or voice recognition, or a physical token that is only accessible to the user.
Each type of authentication has its own unique set of security features, which are dictated by a variety of factors, including regulatory requirements, the sensitivity of the data being protected, and the threats that are most likely to be encountered.
Biometric authentication is a form of authentication which utilizes biometric technology and the user's physical characteristics, such as finger- or palm prints, facial features, or even voice recognition to identify and verify their identity. It can be used for access control and data security purposes, as a means of ensuring secure access to systems and applications.
The best authentication method is one that is most effective in establishing the identity of an individual or entity. Multi-factor authentication (MFA) is a popular approach, as it requires a combination of two or more independent methods for validating identity. This could include something the user knows such as a username/password, something they have such as a physical hardware token, and something they are such as biometrics.
.avif)
Use our product finder to pinpoint the ideal product for your needs.