PRODUCT

Smarter Biometrics, Stronger Digital Identity.
VIEW ALL
product finder
solution
case study
support
Company

Identifying the World. Easily, Securely.


years of solid experience
20+
.jpg)
400+
customised projects



EN
.avif)

Have you ever wondered how secure your authentication methods really are when it comes to granting access to your digital assets or physical premises? In an era where security breaches and identity theft are rampant, understanding authentication factors is not just an IT buzzword—it's an essential part of how we protect assets and verify identities.
This comprehensive guide is your one-stop resource to understand the five core authentication factors, from traditional ones like passwords and PINs to innovative solutions like biometrics. We will also look at practical considerations for selecting authentication factors and discover the unique benefits of using biometrics for authentication.
Whether you're looking to secure a digital application or control access to a physical facility, this guide has you covered. Let's get started!
Authentication factors are the distinct categories of credentials used for verifying the user's identity during the authentication process. These factors are critical for controlling both digital and physical access to systems, networks, and facilities.
Whether it's logging into your computer or entering a secured office, the authentication process aims to verify that the user is who they claim to be. In a broader sense, authentication factors are the bedrock of security protocols designed to protect against unauthorized access and malicious actors.
The choice of authentication factors can greatly impact an organization's ability to protect its assets while balancing user convenience and compliance requirements.
Here's a brief overview of the authentication fundamentals:
Authentication is the procedure to confirm that an entity—usually a user attempting to gain access to a secured network or physical location—is indeed who they claim to be. Various authentication methods and factors are used depending on the level of security needed.
In the realm of security, both digital and physical, the criteria or factors used for authentication can largely be broken down into five types. These types each serve their own unique purpose in verifying a user's identity and can be used in various combinations for more secure access. Below are the categories that cover the breadth of this authentication landscape:
When it comes to authentication, one size doesn't fit all. The complexity of your authentication process can vary depending on your specific security needs, from the simplest form of single-factor authentication to the more robust multi-factor approaches.
In the landscape of authentication factors, biometrics are rapidly carving out a pivotal role. Traditionally, authentication relied heavily on knowledge and possession factors—like passwords and smart cards—to confirm a user's identity. However, as the need for more robust security escalates, the limitations of these traditional factors become increasingly apparent.
What makes biometrics particularly impactful is their role in multi-factor authentication. When combined with other factors like something you know (passwords) or something you have (security tokens), biometrics serve as an additional authentication factor in a multi-layered security system, making it both secure and user-friendly. From fingerprint scans in smartphones to facial recognition access control at secured facilities, the application of biometric authentication is increasingly versatile and reliable.
Understanding authentication factors is key for a comprehensive security strategy. Whether you're a developer configuring an authentication request for an app, or a security officer concerned with access control in a corporate building, you'll need to choose from multiple factors. Your choice influences how effectively you can verify the user's identity and how robust your security will be against potential breaches.
Now that we've laid the groundwork, in the next section, we'll dive into the details of the five key authentication factors that form the backbone of any robust security strategy, both online and offline. Special attention will be given to biometrics, shining a light on their unique advantages and practical applications.
Understanding the diverse landscape of authentication factors is the foundation of building a robust security system. The five key types of factors: Knowledge-Based, Possession-Based, Inherence-Based, Location-Based, and Behavior-Based, offer various ways to confirm a user's identity.
Whether you're tasked with safeguarding a digital system or limiting physical access to a facility, grasping the nuances of these five factors will empower you to make informed decisions. Here’s a closer look at each:
Knowledge-based factors are the foundation of most authentication systems. They represent the information only you should know.
While knowledge factors are easy to implement, they are vulnerable to various forms of attacks, including phishing and social engineering. Thus, they are often combined with other factors in multi-factor authentication systems for enhanced security.
Possession-based factors validate a user's identity by requiring a physical object that only the legitimate user should have, adding another layer to the authentication process.
These are just a few examples. Possession factors add complexity to the authentication process, making it more challenging for unauthorized users to gain access. However, while these factors enhance security, they can still be vulnerable, especially if the possession item is lost or stolen.
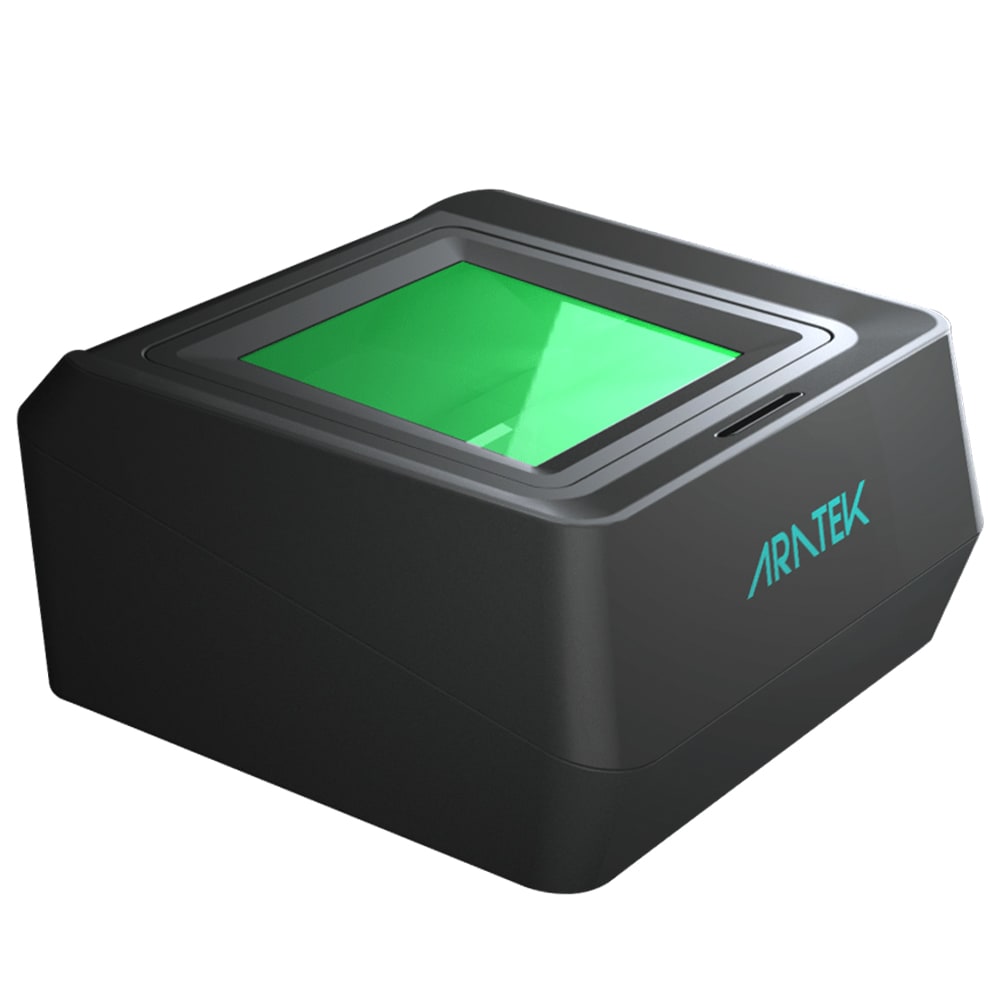
In modern-day authentication, inherence-based factors, which are also referred to as biometrics, are increasingly gaining popularity. These factors are derived from your distinctive physiological traits, and are rapidly becoming the preferred choice for authentication due to their potent combination of robust security and user convenience.
Biometric authentication offers a unique blend of security and user-friendliness, making these inherence-based factors an increasingly popular choice in multi-factor authentication methods.
Location-based factors take into account the geographical location of the user attempting to gain access, offering a unique angle to authentication.
Location-based factors are generally supplemental but can provide an added layer of security for specific applications such as network access restrictions, remote work verification, and enhanced mobile banking security.
These are relatively new and less common but are growing in popularity due to their ability to continuously authenticate users based on behavior.
Behavior-based factors are still evolving but hold great promise in the context of multi-factor authentication, especially when combined with biometric systems and other traditional factors.
Understanding these five key authentication factors offers a comprehensive view into the choices available for securing both digital and physical environments. In the following section, we'll dive into practical considerations for choosing the right combination of these factors to meet your specific security needs.
After acquainting ourselves with the broad spectrum of authentication factors, the next critical juncture is applying this understanding in a practical setting. Whether you are a system administrator, a business owner, or a concerned individual, the choices you make here could substantially impact both your security and user experience. So, how do you go about picking the right combination of authentication factors?
It's essential to understand the risk level associated with what you are protecting, be it a data center or a restricted area within a facility.
Regardless of the environment, the ease with which users can authenticate themselves is critical to system compliance and overall satisfaction.
The costs, both financial and in terms of complexity, can vary widely based on your choice of authentication factors.
The factors you choose should be versatile enough to handle various situations and scalable to meet future requirements.
Compliance isn’t just a box to tick; it's an ongoing responsibility that has both legal and financial implications.
Choosing the right authentication factors isn’t just a question of selecting the most advanced technologies available. It’s about finding a tailored solution that fits your specific needs and constraints. The ideal choice often involves a mix of factors, sometimes even from the same category, to create a robust multi-factor authentication system that balances user convenience with high-level security. So, whether you are managing access to a secured network or a mobile app, keep these practical considerations at the forefront of your decision-making process.
So you've absorbed the key considerations for selecting authentication factors. The next logical step is to put this information into action. To guide you through the decision-making process, we've curated a checklist along with pertinent questions to ponder. Each point is designed to help you craft a robust authentication strategy that is both secure and user-friendly.
By meticulously walking through this checklist and considering these questions, you'll be well-equipped to make informed decisions about which authentication factors are most suitable for your needs. Whether you're fortifying a digital platform or enhancing the security of a physical space, the right blend of authentication factors can make all the difference.
Authentication factors stand as the guardians of access, whether in the digital realm or the physical world. From the familiar passwords to the futuristic biometric scans, the spectrum of choices available for securing your data and spaces is vast. By understanding the unique attributes of each authentication factor and considering practical implementation, you can forge a secure environment that also values user experience.
As you embark on your journey to fortify security, remember that one size doesn't fit all. It's about finding the right blend of factors that align with your organization's risk profile, user needs, and compliance requirements.
Ready to take the next step toward a more secure future? Contact us today to explore how our biometric solutions can elevate your security landscape while ensuring an intuitive user experience.
.avif)
Use our product finder to pinpoint the ideal product for your needs.